📚 Solved Questions of previous year Operating system
Section - A
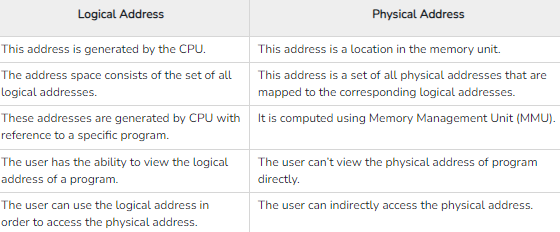
Q-1 Name two difference between logical and physical addresses.
(Year -2016,2018)
A logical address is the virtual address that is generated by the CPU. A user can view the logical address of a computer program. On the other hand, a physical address is one that represents a location in the computer memory. A user cannot view the physical address of a program.
source
Q-2 What is preemptive and non-preemptive scheduling? Explain
(Year -2016)
Preemptive scheduling
Preemptive scheduling is a method that may be used when a process switches from a running state to a ready state or from a waiting state to a ready state.
The resources are assigned to the process for a particular time and then removed. If the resources still have the remaining CPU burst time, the process is placed back in the ready queue. The process remains in the ready queue until it is given a chance to execute again.
Non-preemptive
Non-preemptive scheduling is a method that may be used when a process terminates or switches from a running to a waiting state.
When processors are assigned to a process, they keep the process until it is eliminated or reaches a waiting state. When the processor starts the process execution, it must complete it before executing the other process, and it may not be interrupted in the middle.
Q-3 Which are the four conditions that causes the occurrence of a deadlock? Explain.
(Year -2016)
When a process requests for the resource that is been held another process which needs another resource to continue, but is been held by the first process, then it is called a deadlock.
There are four conditions because of which Deadlock is going to occur in Operating Systems. The Conditions are:
- Hold and Wait
- No Pre Emption
- Mutual Exclusion
- Circular Wait
Q-4 What are the functions of device management
(Year -2016)
Device Management in Operating system manages all the hardware or virtual devices of a computer or PC. The device management system allocates input/output devices to the process on the basis of priority and deallocated as well either temporarily or permanently depending upon the conditions.
The function of device management are:-
- open and close device drivers
- communicate with device drivers
- control and monitor device drivers
- write and install device drivers
Q-5 Explain the concept of system protection and security
(Year -2016)
System protection in an operating system refers to the mechanisms implemented by the operating system to ensure the security and integrity of the system. System protection involves various techniques to prevent unauthorized access, misuse, or modification of the operating system and its resources.
Q-6 What is an operating system?Discuss the various services of the os.
(Year -2018)
An operating system (OS) is the program that, after being initially loaded into the computer by a boot program, manages all of the other application programs in a computer
Following are a few common services provided by an operating system −
- Program execution
- I/O operations
- File System manipulation
- Communication
- Error Detection
- Resource Allocation
- Protection
Q-7 Difference between time sharing system and real time system.
(Year -2018)
A time-sharing operating system is an operating system design that allows multiple users or processes to concurrently share the same system resources, such as the CPU, memory, and peripherals.read in detail
A real-time operating system (RTOS) is an operating system that is used in computing systems that needs strict completion deadlines for all the tasks that need to be performed on it.
Explain the demand paging and cache memory.
(Year -2018)
Demand paging is a technique used in virtual memory systems where the pages are brought in the main memory only when required or demanded by the CPU.
Cache memory is a chip-based computer component that makes retrieving data from the computer's memory more efficient. It acts as a temporary storage area that the computer's processor can retrieve data from easily.
Explain the various attributes of a file.
(Year -2018,2022)
Attributes of the File
Name
Every file carries a name by which the file is recognized in the file system. One directory cannot have two files with the same name.
Identifier
Along with the name, Each File has its own extension which identifies the type of the file. For example, a text file has the extension .txt, A video file can have the extension .mp4.
Type
In a File System, the Files are classified in different types such as video files, audio files, text files, executable files, etc.
Location
In the File System, there are several locations on which, the files can be stored. Each file carries its location as its attribute.
Size
The Size of the File is one of its most important attribute. By size of the file, we mean the number of bytes acquired by the file in the memory.
ProtectionThe Admin of the computer may want the different protections for the different files. Therefore each file carries its own set of permissions to the different group of Users.
Time and Date
Every file carries a time stamp which contains the time and date on which the file is last modified.
What is purpose of system calls?
(Year -2022)
A system call is a way for programs to interact with the operating system. A computer program makes a system call when it makes a request to the operating system’s kernel. System call provides the services of the operating system to the user programs via Application Program Interface(API).
What is the principle advantage of multiprogramming?
(Year -2022)
Advantages of multiprogramming are −
- Increased CPU Utilization − Multiprogramming improves CPU utilization as it organizes a number of jobs where CPU always has one to execute.
- Increased Throughput − Throughput means total number of programs executed over a fixed period of time. In multiprogramming, CPU does not wait for I/O for the program it is executing, thus resulting in an increased throughput.
- Shorter Turn around Time − Turnaround time for short jobs is improved greatly in multiprogramming.
- Improved Memory Utilization − In multiprogramming, more than one program resides in main memory. Thus memory is optimally utilized.
- Increased Resources Utilization − In multiprogramming, multiple programs are actively competing for resources resulting in higher degree of resource utilization.
- Multiple Users − Multiprogramming supports multiple users.
What is hard and soft semaphore?
(Year -2022)
Semaphores are integer variables that are used to solve the critical section problem by using two atomic operations, wait and signal that are used for process synchronization.
Type-1: General Semaphore
A semaphore whose integer component can take arbitrary non-negative values of S.L. these is called General Semaphore. They are kind of weak semaphores.
Type-2: Binary Semaphore
A semaphore whose integer component S.L. takes only the values 0 and 1 is called a binary semaphore. This is also known as “mutex” which stands for mutual exclusion.
Type-3 : Strong Semaphore
In Strong semaphores, S.L. remains unchanged as in weak semaphores whereas S.V. is replaced by the queue. Because removal of arbitrary process in a weak semaphore it may lead to starvation whereas in this case, it remains free from starvation.
Type-4 Busy- Wait for Semaphore
It does not have a component S.L. and Semaphore S is identified only by S.V. Busy-Wait Semaphore are appropriate in a multi-processor system where the waiting process has its own processor and is not waste CPU time that could be used for computation.
How measure reliability of H/W disk?
(Year -2022)
Hardware reliability is defined as the probability of the absence of any hardware-related system malfunction for a given mission.
- Tests based on the customer’s study of FMEA.
- Accelerated testing, including HALT/HASS, that run the part repeatedly with no deadtime between cycles, in either static or dynamic environmental conditions.
- Pre-process test results for the customer so they can perform “Reliability growth analysis”.
- Measured part performance while it is being subjected to thermal-induced, shock and vibration fatigue analysis.
- Continuous cycling a specific profile to simulate actual use, while changing that profile randomly. The profile can be for load, temperature, speed, and so forth.
Section-B
Describe the following allocation algorithms in the context of contiguous allocation:
(i) First fit
(ii) Best fit
(iii) Worst fit
(Year -2016)
First Fit
In the first fit approach is to allocate the first free partition or hole large enough which can accommodate the process. It finishes after finding the first suitable free partition.
Advantage
Fastest algorithm because it searches as little as possible.
Disadvantage
The remaining unused memory areas left after allocation become waste if it is too smaller. Thus request for larger memory requirement cannot be accomplished.
Best Fit
The best fit deals with allocating the smallest free partition which meets the requirement of the requesting process. This algorithm first searches the entire list of free partitions and considers the smallest hole that is adequate. It then tries to find a hole which is close to actual process size needed.
Advantage
Memory utilization is much better than first fit as it searches the smallest free partition first available.
Disadvantage
It is slower and may even tend to fill up memory with tiny useless holes.
Worst fit
In worst fit approach is to locate largest available free portion so that the portion left will be big enough to be useful. It is the reverse of best fit.
Advantage
Reduces the rate of production of small gaps.
Disadvantage
If a process requiring larger memory arrives at a later stage then it cannot be accommodated as the largest hole is already split and occupied.
What is deadlock? Discuss the method for handling deadlocks.
(Year -2016)
Deadlock is a situation where a process or a set of processes is blocked, waiting for some other resource that is held by some other waiting process.
Methods of handling deadlocks: There are four approaches to dealing with deadlocks.
- Deadlock Prevention
- Deadlock avoidance (Banker's Algorithm)
- Deadlock detection & recovery
- Deadlock Ignorance (Ostrich Method)
Deadlock Prevention: The strategy of deadlock prevention is to design the system in such a way that the possibility of deadlock is excluded
Deadlock Avoidance: The deadlock avoidance Algorithm works by proactively looking for potential deadlock situations before they occur. It does this by tracking the resource usage of each process and identifying conflicts that could potentially lead to a deadlock.
Deadlock Detection: Deadlock detection is used by employing an algorithm that tracks the circular waiting and kills one or more processes so that the deadlock is removed.
Deadlock Ignorance: In the Deadlock ignorance method the OS acts like the deadlock never occurs and completely ignores it even if the deadlock occurs.
what is disk Scheduling? Define various types of disk scheduling
(Year -2016)
Disk scheduling is done by operating systems to schedule I/O requests arriving for the disk. Disk scheduling is also known as I/O scheduling.
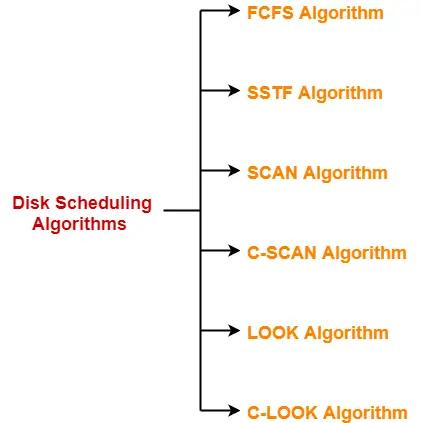
FCFS disk scheduling algorithm:
It stands for 'first-come-first-serve'. As the name suggests, the request which comes first will be processed first and so on.
SSTF disk scheduling algorithm:
It stands for 'Shortest seek time first'. As the name suggests, it searches for the request having the least 'seek time' and executes them first.
SCAN disk scheduling algorithm:
In this algorithm, the head starts to scan all the requests in a direction and reaches the end of the disk. After that, it reverses its direction and starts to scan again the requests in its path and serves them. Due to this feature, this algorithm is also known as the "Elevator Algorithm".
C-SCAN disk scheduling algorithm:
It stands for "Circular-Scan". This algorithm is almost the same as the Scan disk algorithm but one thing that makes it different is that 'after reaching the one end and reversing the head direction, it starts to come back.
LOOK the disk scheduling algorithm:
In this algorithm, the disk arm moves to the 'last request' present and services them. After reaching the last requests, it reverses its direction and again comes back to the starting point. It does not go to the end of the disk, in spite, it goes to the end of requests.
C-LOOK disk scheduling algorithm:
The C-Look algorithm is almost the same as the Look algorithm. The only difference is that after reaching the end requests, it reverses the direction of the head and starts moving to the initial position. But in moving back, it does not serve any requests.
Describe the critical section problem with suitable example.
(Year -2018)
The critical section is a code segment where the shared variables can be accessed. An atomic action is required in a critical section i.e. only one process can execute in its critical section at a time. All the other processes have to wait to execute in their critical sections.
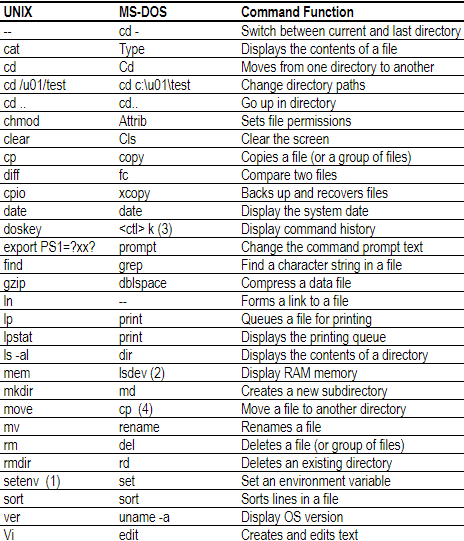
Write the five UNIX and DOS commands with cross reference and function
(Year -2018)
Explain how memory can dynamically allocated using first fit,
best fit and worst fit strategies
(Year -2018)
watch Video to clear concept
Q on a system using paging and segmentation, The virtual address spaceconsists of up to 8 segments where each segment can be up to 229 bytes long. The hardware page each segment into 256bytes pages. HOw many bits in the virtual address specify the:
(a) Segment number
(b) Page number
(c) Offset within Page
(d) Entire virtual address
(Year -2022)
Q Discuss characteristics of device which effect on supervisor call interface?
(Year -2022)
A supervisor call is an instruction sent to a computer’s processor that directs it to transfer computer control to the operating system’s supervisor program
supervisor call (SVC) instruction is a processor instruction that directs the processor to pass control of the computer to the operating system's supervisor program.
Q What methods determines how a file's records are allocated into blocks?
The allocation methods define how the files are stored in the disk blocks. There are three main disk space or file allocation methods.
- Contiguous Allocation
- Linked Allocation
- Indexed Allocation
The main idea behind these methods is to provide:
- Efficient disk space utilization.
- Fast access to the file blocks.
(Year -2022)
section-c
Q-9 (a )what is an operating system ? Discuss the role of an operating system
(Year -2016)
(b) what is memory segmentation?How is it different from paging?
(Year -2016)
Q-10 (a) explain semaphore.
(Year -2016)
(b) Explain with examples of your own,the following any two process scheduling algorithm
(i) First Come First Serve
(ii) Shortest Job First
(iii) Priority Scheduling
(iv) Round Robin
(Year -2016)
Q-11 (a) Define Resource Allocation Graph Give that, there is only one instance of each resouce type,
(Year -2016)
describe the resouce allocation graph algorithm for deadlock avoidance using a suitable example.
(Year -2016)
(b) Discuss the procedure for avoiding a deadlock situation. Also describe the procedure to achieve safe state.
(Year -2016)
Q-12 (a) Explain the different techniues to improve disk reliability.
(b) Explain the different activities performed by disk management
(Year -2016)
Q-13 (a) consider the following page reference string:
1,2,3,4,2,1,5,6,2,1,2,3,7,6,2,1,2,3,6
How many page fault would occur for the followng replacement algorithms, assuming four frames?
(i) LRU replacement
(ii) FIFO replacement
(iii) Optimal replacement
(Year -2016)
(b) Describe the following with suitable example:
(i) Directory structure
(ii) Free space management
(Year -2016)
Q (a) What is page frame and page fault?
(Year -2018)
(b) Solve:
7,0,1,2,0,3,0,4,2,3,0,3,2,1,2,0,1,7,0,1
using FIFO and LRU algorithm and calculate the page fault,page from =3
(Year -2018)
Q 10 Define the following
(i) Fragmentation
(ii) Paging
(iii) Process state
(iv) Segmentation
(V) Memory management system
(Year -2018)
Q what is deadlock ? Explain four necessary conditions for deadlock to
occur with suitable example . Describe the different methods for
prevention and avoidance of deadlocks.
(Year -2018)
Q Explain the linked allocation method for file. List the
merits and drawbacks of this method. How does an indexed allocation
solve the problems of linked allocation scheme?
(Year -2018)
Q Define multiprocessor system. What are difference between symmetric and asymmetric multiprocessing?
Explain advantages and disadvantages of multiprocessor systemes?
(Year -2022)
Q Write short notes of following :
(a) Deadlock Prevention
(b) Disk Swap-space management
(c) Real time system
(d) page replacement
(Year -2022)
Q (a) What Computer Bus?Different list different type of Bus.
(Year -2022)
(b) What is architecture of Peripheral Component Interconnect Bus?
(Year -2022)
Q What is demand paging? How page fault occures? What are factors
that affect the determination of the page size?
(Year -2022)
Q What is Thread ? Discuss different approaches for implementation of Process Threads.
(Year -2022)
bcanotes bca notes bcaquestionpaper
bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca bcanotes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper
bcanotes bca notes bcaquestionpaper bca questionpaperbcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaperbcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper ccsu ccsunotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes
Visit W3Schools.com!Visit W3Schools.com!Visit W3Schools.com!Visit W3Schools.com!Visit W3Schools.com!Visit W3Schools.com!Visit W3Schools.com!Visit W3Schools.com!Visit W3Schools.com!ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes bcanotes bca notes bcaquestionpaper bca questionpaper
bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper
ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes
ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes
bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper
bcanotes bca notes bcaquestionpaper bca questionpaperbcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaperbcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes
ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes bcanotes bca notes bcaquestionpaper bca questionpaper
bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper
ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes
ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes
bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper
bcanotes bca notes bcaquestionpaper bca questionpaperbcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaperbcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes
ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes bcanotes bca notes bcaquestionpaper bca questionpaper
bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper
ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes
ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes
bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper
bcanotes bca notes bcaquestionpaper bca questionpaperbcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaperbcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes
ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes bcanotes bca notes bcaquestionpaper bca questionpaper
bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper bcanotes bca notes bcaquestionpaper bca questionpaper
ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes
ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaper ccsubcanotes ccsu bca cccsu notes ccsubcaquestionpaper bca questionpaperbcanotes
